Analytics

Modern Blueprint to Insider Threat Management
Taking a People-Centric Approach to Your Insider Threat Management (ITM) Programme. Insider threats can...

Three Top Trends in Higher Ed IT for 2021 and Beyond
We've had a tough 2020, but the ability to work and learn online from anywhere has been popular with...
5 Best Practices for CISOs Adopting XDR
The pace of change in IT infrastructures is unyielding. With XDR, cybersecurity teams can keep up, improve...

Guide to Transform Your Network with Advanced Load Balancing
To evolve with the times and deliver capacity to the business, network ops teams are transforming the...

Why IT Struggles with Innovation and What to Do About It
Just 21% of senior IT professionals believe that they address change better than their competitors, according...

Security Starts Here: Privileged Access Management
The threat of a security incident or critical error is very real, and it's something that auditors are...

Getting Faster: Know Your Website, and Know What's Slowing It Down
Speed and performance of your website significantly impact revenue growth and conversions. The numbers...
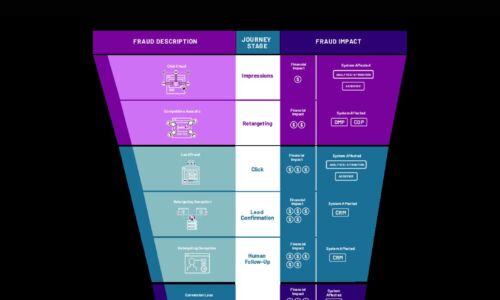
Cybercrime Threatens the Digital Funnel
Cybercriminals are employing new attack methods on new digital surfaces, including digital marketing....

Security Considerations in Industrial 5G Environments
The convergence of market demand and new digital capabilities is helping companies transform their operations....

How Low-Code Can Supercharge Application Development
At a time of disruption and uncertainty, with more disruption and uncertainty to come, businesses must...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.



