Applications

Activate ESG Use Case Guide
Incorporating robust ESG practices into business strategy and execution is critical, not only to be a...
NIST Cybersecurity Framework
The document gives you an overview of the NIST Cybersecurity framework, an internationally widespread...
A Buyer's Guide to Audit Management Software
For today's internal audit teams, the audits themselves are only one part of a growing scope of responsibilities. Executives...
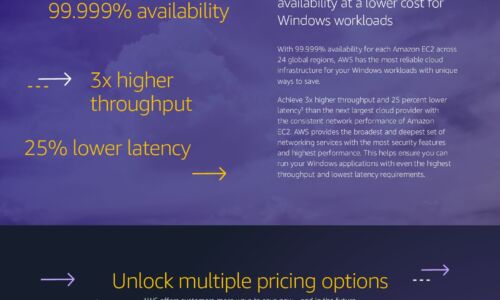
Windows Cost Savings Infographic
Save by moving Windows workloads to AWS Companies can lower infrastructure costs while improving performance,...

Book of Knowledge for Customer Experience
Technology is always evolving, and customer expectations are evolving with it. ServiceNow is helping...

Dell EMC Storage for Microsoft SQL Server
Microsoft SQL Server environments span many versions in a typical data center, running both traditional...

Workday for the Hospitality Industry
With change the only constant today, hospitality leaders need a better way to accelerate digital transformation...
The CIO’s Guide to Transformation with AppExchange
A huge part of a CIO's role is 'keeping the lights on'. They are responsible for making sure systems...

Compromise Assessment Use Cases
With cyber attacks increasing both in quantity and sophistication, how can an organization know with...
Making the Grade: End-to-End Security in Education
While students are preoccupied with completing online school assignments and streaming educational videos,...

SASE: Beyond the Hype
Solve network and security management challenges with a Secure Access Service Edge architecture This...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.