BYOD
The CIO's Guide to Cloud Data Management
Data is power. How you use it and how you protect it is critical. As a CIO, you are responsible for leading...

4 Low-Code Best Practices for SAP Fiori Apps
It has been proven that enterprise IT teams that include a no-code/low-code approach for their SAP app...
How Effective Retailers Balance Customer Engagement and PCI Compliance
For CIOs of retail organizations, compliance with Payment Card Industry (PCI) standards is a top concern,...
Cost of Insider Threats 2020 Report
The key takeaway is that, across all three insider threat types outlined above, both the frequency and...

5 Reasons to Make the Shift to Cloud-Managed Networking
Cloud has proven advantages for the enterprise. Modernizing IT with cloud apps, compute, and storage...
Ponemon Cost of Insider Threats Report 2022
External attackers aren't the only threats modern organisations need to consider in their cybersecurity...

5-minute Primer: MultiLine at Work
What do you do when your employees conduct company business on their personal devices? On one hand, it...
User Risk Report 2018
Risky end-user behaviours are impacting organisations around the world, with implications that can be...

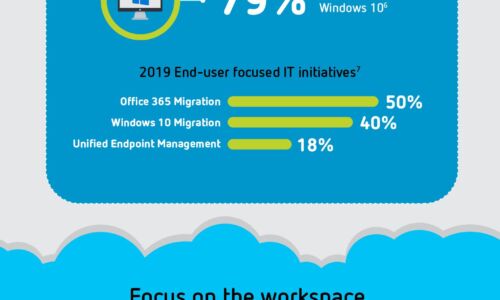
How a Hybrid Cloud Approach Supports Top IT Trends
Digital disruption is impacting every industry, and businesses understand that they need to adjust to...

Three reasons to manage Office 365 with Citrix Workspace
Are you considering migrating to Microsoft Office 365 or already facing challenges with the move? Don't...
Automated Endpoint Incident Response: An Enterprise Guide
Strong cybersecurity has always been an essential component of a company's digital transformation success....
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.