Cloud Computing
Respond and Evolve with Your Multi-Cloud
In a world of uncertainty, organizations on traditional IT platforms need something they can rely on...

Power Platform Jumpstart
The Cognizant Microsoft Business Group takes you through automation journey possibilities, demonstrating...

Top 3 challenges your team faces when building in the cloud
Learn the root causes of the challenges your cloud and security teams are facing and see how these challenges...

Office of the CTO Report: Continuous API Sprawl
APIs are a contract between the service provider and service consumer. When any application uses an API,...
Trusted Access Report
As global conflicts spill into the digital realm, protecting people through to the enterprise is increasingly...

State of the Phish 2019 Report
What did the phishing landscape look like in 2018? Is general end-user awareness of phishing and other...
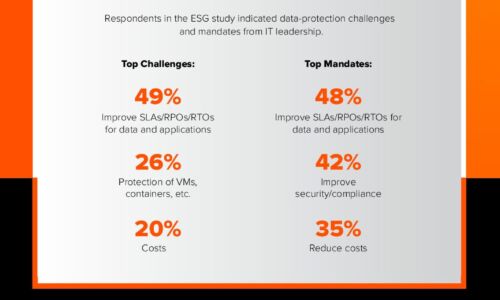
Close the Data Availability Gap
A recent ESG survey of over 1,000 global IT decision-makers found that 82% of enterprises are facing...

Modern Storage Accelerates Data Insights, Speeding Innovation
Deep learning opens up new worlds of possibility in artifi cial intelligence, enabled by advances in...
A Guide to Replacing Antivirus with Advanced Endpoint Security
Cyberattacks are rapidly evolving. It is more critical than ever that your company be protected by the...

Solving the Talent Puzzle
The top five percent of professional services organizations (PSOs) are experiencing low levels of attrition,...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.