Cloud Computing
Intelligent Master Data Management For Dummies
Intelligent Master Data Management For Dummies, Informatica Special Edition, consists of five chapters...

Best-in-Class SaaS Performance
The average person uses 36 cloud-based services every single day. Now it's up to IT operations teams,...

Seamless and Simple Migration to the Cloud
Applications are the heart of every modern organization. As digital transformation becomes increasingly...
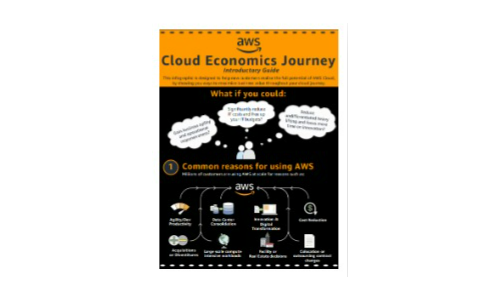
AWS Cloud Economics Introductory Guide
Discover the full potential of AWS Cloud and ways to maximise business value with this infographic. ...
Unlock the Power of Hybrid Cloud with Consistent Operations eBook
Embracing a hybrid cloud operating model creates new possibilities for IT organizations, paving the way...
Networking and Information Systems (NIS) Directive
The NIS Directive has been designed to work alongside data protection legislation. It will be governed...
NoSQL for Dummies
This easy to read guide to NoSQL databases provides the type of no–nonsense overview and analysis that...

The New World of Digital Workplace Services
What if you could rapidly digitise key employee processes to better engage and delight your employees,...
Why It Pays to Use Electronic Signature
In today's intensely competitive marketplace, the business world is moving rapidly to online transactions...

Evaluating the Economic Benefits of a Modern Client Strategy
Since working from home became the new normal, work has become something one does rather than someplace...

Why aren't factories as smart as they could be?
Data is revolutionizing manufacturing. Combined with powerful tools like artificial intelligence/machine...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.