Cloud Security

Get Cloud-Ready with SD-WAN
An enterprise-grade SD-WAN solution gives you the ability to realize the speed and agility you need to...

Cyber Attack Trends: Check Point's 2022 Mid-Year Report
The war in Ukraine has dominated the headlines in the first half of 2022 and we can only hope that it...

7 Experts on Moving to a Cloud-based Endpoint Security Platform
Without a doubt, endpoint security has become an urgent priority for many organizations, and it's not...

What is Zero Trust? (Really)
Over the last decade, cybersecurity has been focused on the challenge of securing increasingly vulnerable...

10 Endpoint Security Problems and How to Solve Them
Companies are facing massive cybersecurity challenges – many of which are rooted in the endpoint. In...

Start your data modernization journey
Take the complexity out of your data infrastructure. For organizations running legacy data infrastructure...
Securely Enabling a Hybrid Cloud in Microsoft Azure
The public cloud has rapidly moved past the novelty, curiosity stage to the business critical initiative...
The Gorilla Guide to Achieving IT Asset Management Success
ITAM is about knowing what you've got, where it is, who's using it and how much it costs. If you want...

Enabling Manufacturing Innovation Through the Use of Cloud
In this whitepaper, research firm IDC dives deep into manufacturing use cases in the cloud, evaluates...
Implementing Zero Trust Best Practices
Network security challenges have evolved significantly over the years as users have become increasingly...

Cloud and Web Attacks
A Cloud Security Alliance Research Report Work environments have undergone rapid but lasting changes...
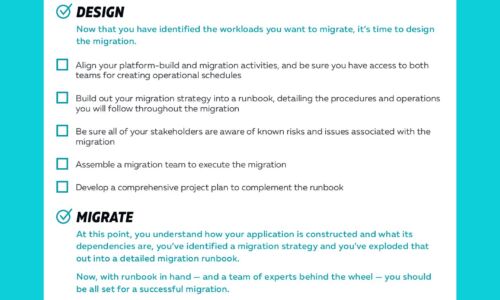
Cloud Migrations Checklist
Cloud migrations can be complex. The key to a successful migration lies in the planning. To help, we've...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.

