Cloud Storage
A CDO’s Guide to Customer Intelligence
To say that the role of the Chief Data Officer (CDO) has evolved quickly is an understatement. Created...
The Data Breach is Coming from Inside the House
Real-Life Tales of Data Loss, Insider Threats and User Compromise Data doesn't lose itself. People lose...

6 Ways a Better Network Helps Offices Grow Stronger, Faster
With the changes in the economic climate and shifts to remote work, we can all confidently agree that...
2021 Email Threat Report: It Started Out With a Phish
Our 2021 Email Threat Report analyzes the top threats seen over a period of a year across organizations...
5 Ways that SD-WAN Transforms your Network
SD-WAN transforms your network by making it more responsive, providing greater bandwidth and being more...
Cloud Computing for Dummies
Cloud computing is a topic that technology pros need to know to stay ahead of the computing game. Cloud...
Cloud Security Fundamentals
Protecting a cloud environment requires a dedicated, comprehensive effort across the policies, processes,...
An Overview of Insider Threat Management
As organistions move towards a more distributed workforce, the traditional perimeter of the office network...
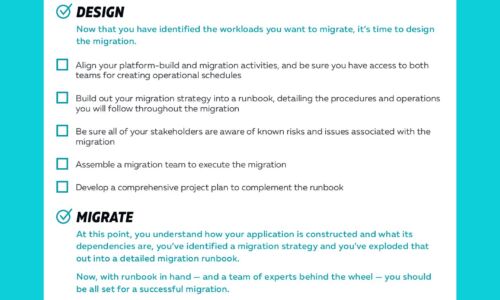
Cloud Migrations Checklist
Cloud migrations can be complex. The key to a successful migration lies in the planning. To help, we've...

NetBackup is Unified Data Protection for the Cloud-Ready Enterprise
As technology evolves, so does NetBackup. This eGuide explores four key use cases that show how NetBackup...
Transforming Security in the Mobile Cloud Era
In the age of digital transformation, maintaining secure interactions among users, applications, and...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.


