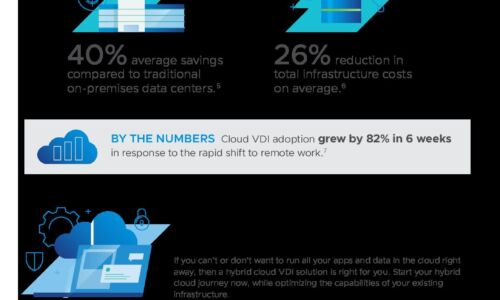
Cloud
Modernize the workforce experience
It's more than a concept, it's our approach to modernizing your workforce. Our products, solutions and...
Use Case-Driven Cloud Security Evaluator Guide
Researching cloud security? Be sure you evaluate yourself and your vendors on the 6 most common cloud...

Adaptive Cloud Security for AWS
Amazon Web Services (AWS) is the largest provider of cloud computing services worldwide. AWS pioneered...

5G Technology Transformation Explained
With the 5G era commencing, service providers must ensure that their infrastructures have the cloud-native,...
Ponemon Cost of Insider Threats Report 2022
External attackers aren't the only threats modern organisations need to consider in their cybersecurity...
Debunking the Top 5 Myths About Malicious Bots
Today, as much as 40% of all Internet traffic consists of bots: non-human users that perform automated...
Red Hat for cloud-native development
Application development is a complicated undertaking that requires a complex environment and tools. With...
Forrester Wave, We’re a leader!
VMware Carbon Black Named a Leader in The Forrester Wave™: Endpoint Security Software As A Service,...

Winning in the New Era of Data Management
In the data-driven age, information is as valuable as currency. Entire industries are being disrupted...

Eight Digital Best Practices for Procurement Professionals
Industry experts predict that successful businesses will soon become 100% digital for all transactions....
Secure Beyond Breach
Securing the perimeter is no longer enough. The focus has shifted to ensuring your organization continues...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.