Cloud
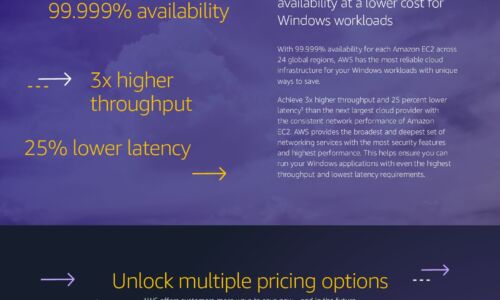
Windows Cost Savings Infographic
Save by moving Windows workloads to AWS Companies can lower infrastructure costs while improving performance,...

A New Trend Explained: What is Multicloud?
Multicloud has become one of the buzzwords of modern IT, yet there's a lack of agreement on what it actually...
How Zendesk Uses Slack
When technology is the core of your business, managing risk is a 24/7 concern. There are the big, infrastructural...

Migrating to the Public Cloud: Three Success Stories
Organizations find the public cloud appealing for its promises of agility, reduced costs and developer-friendly...

University of Surrey's Edification for its Cyber Protection
The University of Surrey is a public research university in Guildford, England, receiving its royal charter...

Modernize Your Legacy Applications in the Cloud
In the last year, enterprises and industries of all kinds faced rapidly changing business environments...

Book of Knowledge for Customer Experience
Technology is always evolving, and customer expectations are evolving with it. ServiceNow is helping...

IDC: Strategies for Building Digital Infrastructure Resiliency
Multiple generations of applications. Multiple generations of infrastructure. Is there a way to reduce...
SaaS pricing in uncertain times – 4 things to consider
Software as a Service (SaaS) vendors faces challenges when pricing their services, particularly in the...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.