Data Center
Rapid, Successive and at Scale
Disruption -- whether big (COVID-19) or small (new start-up competitors) -- has more or less become commonplace...

DDoS attack trends for Q2 2021
Cloudflare's network protects approximately 25 million Internet properties, giving us deep insight into...
Forrester : Managing Security Risk and Compliance
The explosion of data and proliferation of devices demands better security tools and monitoring from...
Cyber-resiliency Maturity in Servers
Cyber resiliency is now an essential requirement for any business. Given the threat to data and IT servers,...

Securely Managing Your UNIX Environment
With today's stringent compliance environment, sophisticated and varied threats, and the demand of interoperability...
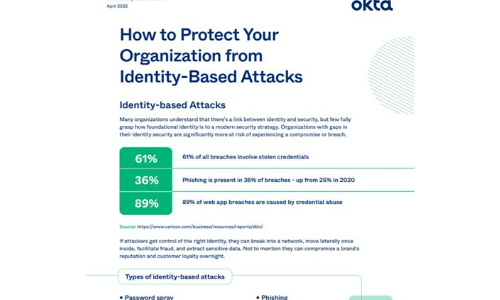
How to Protect Your Organisation from Identity-Based Attacks
Many organizations understand that there's a link between identity and security, but few fully grasp...
Office 365 All-in-One For Dummies
The deepest reference on Microsoft's productivity service Office 365 offers the same productivity power...

Hope is NOT a strategy: Secure your business with the Content Cloud
Seems like every week there's news of another cybersecurity breach. Ponemon Institute has found that...
3 Ways to Make Cloud your Business eBook
The role of IT infrastructure and operations leaders has dramatically changed, and cloud evolution continues...

Making all the right connections
Ask someone how they feel about a company, and they'll have an immediate response. All too often it's...

Simplified Zero Trust Segmentation with Illumio Core
Modern ransomware is one of the most significant cybersecurity threats to critical services, compute...

G2 Mid-Market Endpoint Protection Suites Report
Thinking about investing in endpoint protection and want to get a real sense of how different solutions...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.