Data Center

Protecting The End User
A people-centric approach to managing vulnerability, attacks and privilege. Organisations are spending...
Sotero Data-In-Use Encryption
Though encryption is the most effective way to reduce the probability of a security breach, traditional...

Evaluating the Economic Benefits of a Modern Client Strategy
Since working from home became the new normal, work has become something one does rather than someplace...
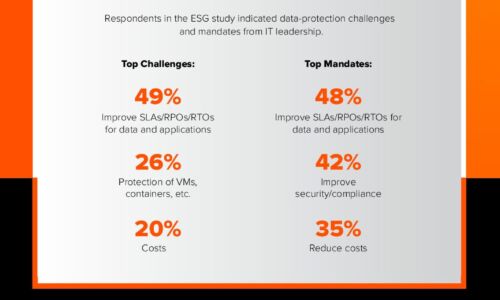
Close the Data Availability Gap
A recent ESG survey of over 1,000 global IT decision-makers found that 82% of enterprises are facing...

Analog Devices Automates its Threat Response Process
Analog Devices (ADI) is a Fortune 100 company and a world leader in the design, manufacture, and marketing...
XDR vs. SIEM: A Cybersecurity Leader's Guide
Security teams are experiencing acute pain with their current solutions. Security information and event...
Investa Adds Micro-Segmentation to Security Portfolio
As one of Australia's largest commercial real estate companies, Investa has a powerhouse portfolio worth...
7 Ways to Work from Anywhere
Bring security and speed to the office of the future Following a massive global influx of remote work,...
Dell Technologies Continuously Modern Storage
IT's role in business has changed. IT organizations were traditionally once viewed as cost centres, but...

IPv6 migration with Micetro by MenandMice
IPv6 adoption has been slow in the corporate world. Despite global IPv6 traffic increasing with 500%...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.