Digital transformation
Big Data for Finance
Across industries, data continues to grow as an extremely valuable resource. This is especially true...
Accelerate your journey to microservices-based applications with Citrix ADC
Today, new application architectures like Devops microservices are opening great opportunities for innovation....

A CDO's Guide to Customer Intelligence
To say that the role of the Chief Data Officer (CDO) has evolved quickly is an understatement. Created...
MLOps: 5 Steps to Operationalize Machine Learning Models
Today, artificial intelligence (AI) and machine learning (ML) are powering the data-driven advances that...
Customer 360 for dummies
Did you know that approximately 300 billion emails are sent every day and that about half of all email...
IT Visibility Gap Study: How Vulnerable is Your IT Estate?
As modern IT networks become more complex and distributed, organizations face mounting pressure to manage...
4 Case Studies Show How IT Can Improve Employee Experiences
Trends Are Shifting, and Expectations Are Rising Over the past 10 years, the way people use technology...

4 Best Examples of Field Service Management
Software Built for the Future. Field service management software is quickly becoming a must-have for...
Zero Trust Access for Dummies
As businesses continue to embrace digital innovation, cloud applications, and the new work-from-anywhere...

Change Communications
Change is the only constant for businesses. Well-planned, formalized change communications are essential. Nearly...
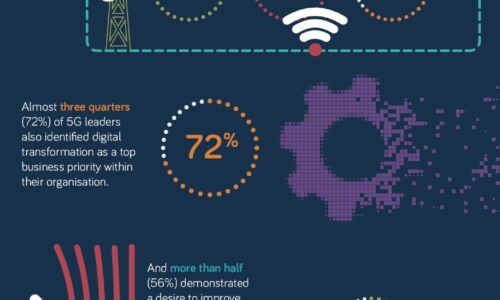
What makes a 5G Leader?
With 5G a still nascent technology, opportunity remains for businesses to accelerate adoption of this...
How chemical companies can achieve a new level of enterprise performance
Mastering the challenges of an ever-evolving enterprise has always been a fundamental part of the day-to-day...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.