Endpoint Security
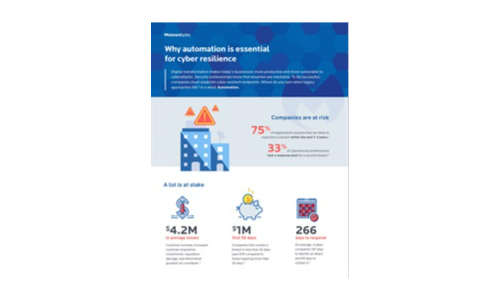
Why automation is essential for cyber resilience
Digital transformation makes today's businesses more productive and more vulnerable to cyberattacks....
The Total Economic Impact™ Of VMware Carbon Black Cloud
Security and IT teams today are constantly dealing with overly complex and siloed toolsets that can't...

Global Threat Landscape Report
Another half-year through unprecedented times has passed. But as unique as these times may feel, we continue...

LogRhythm for SWIFT Customer Security Controls Framework
Society for Worldwide Interbank Financial Telecommunication (SWIFT) facilitates a huge number of financial...
Protect K-12 Schools from Cyberattacks with Active Breach Protection
Ransomware is not just another buzzword. It is a very real threat to educational institutions of all...

Two-Factor Authentication Evaluation Guide
In this guide, you will learn how to evaluate a solution based on: ...

Solve the security puzzle with end-to-end security solutions
As an IT decision maker, you're focused on finding effective solutions you can implement quickly and...

The PC Lifecycle Continuum: From Control to Transformation
As diverse organizations seek to implement data-driven strategies, the personal computer in all its varieties...
Artificial Intelligence: The Smarter Approach To Information Security
The news headlines are replete with stories of devastating data breaches, compromising the personal and...

The CISO's Guide to Ransomware Prevention
Ransomware attacks have transformed the cyber attack landscape. These sophisticated and persistent threats...
Enable End-to-End Zero Trust To Achieve Effective Outcomes
Zero Trust priorities have evolved in 2020 to require solutions that secure your remote workforce with...
Veeam Enterprise Availability for SAP HANA
Enterprise-grade companies uses SAP HANA worldwide, this is the application directly related to customers...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.

