ERP

Hindsight Is 2020 The Pandemic Provides a Wake-Up Call - Report
Hindsight Is 2020 — The Pandemic Provides A Wake-Up Call: Integrated Solutions Future-Proof Organizations. VMware...
Charting a Course to SAP Modernization Success
As enterprises plan their SAP modernization efforts, they are looking for solutions that allow them to...

Delivering On Demand: Momentum Builds Toward Flexible IT
These days, it's well understood that technology has changed the way we manage businesses, serve customers...

The Speed of Change: How Fast Are You?
The pandemic crisis and the impact of lockdown have been a massive shock to the global economy and to...
Don’t Diverge—Converge
Digital acceleration is driving the adoption of hybrid IT architectures. These new hybrid environments...

How Modern Digital Experiences Enable Business Innovation
CIOs are on the hook to speed business processes and workflows that lead to improved customer and employee...
Adaptability: The Missing Stage in Your Corporate Preparedness
Best-in-class retail and consumer organizations don't just respond to change—they stay ahead of it....
A More Effective CIO-CFO Partnership
How are IT leaders achieving success in a changing world? To find out, Deloitte and Workday surveyed...
Workday Enterprise Management Cloud Platform: The Power to Adapt
With market changes, global disruptions, competitive pressures, and rapid innovations in technology,...

DynamoDB Users-Why Switching to Couchbase Will Save You Time and Money
Businesses using the Amazon Web Services (AWS) cloud often store their data in Amazon's DynamoDB database...
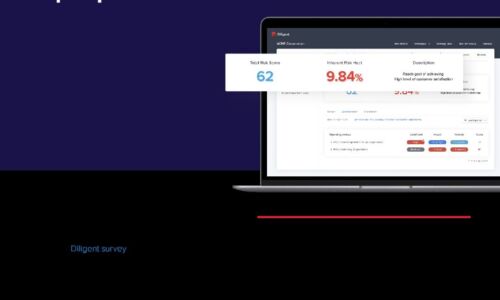
Effective CISO Presentations to the Board: Top Tips & Checklist
As a CISO, you have crucial info to convey about cyber risk, and your board wants to hear it. In a recent...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.