Firewall

Protecting Every Edge To Make Hackers’ Jobs Harder, Not Yours
Today's users need a network that allows them to connect to any resource from any location using any...
Aruba ESP (Edge Services Platform) - Harnessing the Power of the Edge
Every decade or so, we've seen the technology market undergo major shifts. Over the past few decades,...

How to secure your business with the Content Cloud
Hope is NOT a strategy: Secure your business with the Content Cloud Seems like every week there's news...
Strategies for successfully managing privileged accounts
Getting identity and access management (IAM) right for your standard users is hard enough. What about...
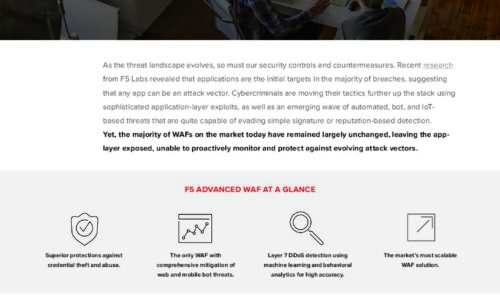
Is Your WAF Keeping Pace with Today’s Advanced Threats eBook
As the threat landscape evolves, so must our security controls and countermeasures. Recent research from...

Take the fight to the cybercriminals
An IT leader's guide to keeping your business running with proactive cybersecurity. It's an incredibly...
Zscaler Private Access as an Alternative to VPN
For almost 30 years, enterprises have relied on the remote access VPN to connect remote users to the...
Data Cataloging for Data Governance: 5 Essential Capabilities
How to drive your enterprise data governance program forward. In today's innovation-driven economy, your...
12 Steps for Stronger Ransomware Protection
Over the last few years, we have signed up hundreds of MSPs. We like to ask every new customer why they...
Unified Communications as a Service
As businesses increasingly embrace a cloud-first strategy, many are migrating their most heavily used...
Reinventing work - New imperatives for the future of working
Following one of the most challenging years in business history, the pandemic has forced every company...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.