Firewall
Q4 in review: The latest DDoS attack vectors
2021 witnessed massive DDoS attacks that demonstrate a trend of intensifying cyber insecurity that affected...

DDos is the New Spam: 3 Strategies to Turn Catastrophe into Annoyance
As DDoS attacks grow larger, more complex, and more pervasive, it can feel like we face a future of inevitable...

Rackspace Fanatical Support for AWS
As organizations move their workloads from traditional data centers to AWS, IT security paradigms are...
Investa Adds Micro-Segmentation to Security Portfolio
As one of Australia's largest commercial real estate companies, Investa has a powerhouse portfolio worth...
Application security, fallacies + realities
The news headlines have been filled with stories about security breaches in recent months. And most of...

Cyber Security for Dummies
Protect your business and family against cyber attacks Cybersecurity is the protection against the unauthorized...

Simplified Zero Trust Segmentation with Illumio Core
Modern ransomware is one of the most significant cybersecurity threats to critical services, compute...
Fortinet Federal Government Cybersecurity Solutions
U.S. federal agencies operate some of the world's largest and most complex digital networks, but many...
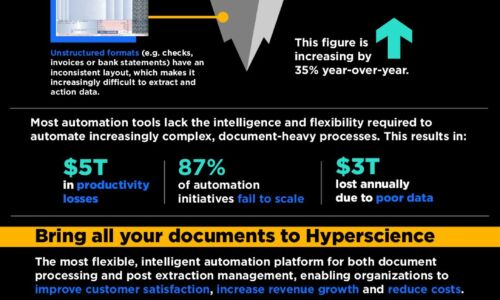
Data to Decisions
If any company still questioned the central importance of data to its future prospects, the last month...

How to Test and Debug Your Mobile Apps in the Cloud
In a heavily fragmented mobile environment, developing applications, which are compatible with multiple...
3 Ways to Reduce the Risk of Data Loss
Amid the fast-moving digital landscape, security risks are on the rise. People, devices, and objects...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.