IT Security

Case Study - Malwarebytes Endpoint Protection and Response
Malwarebytes cut potential downtime to a matter of hours rather than weeks. Malwarebytes complements...

Protecting Data Capital in your Organization
The digital era is changing the way that organizations think about, protect, and monetize data. Now more...
Driving Real Behaviour Change
Today's most potent cyber threat isn't a zero-day vulnerability, new malware or the latest exploit kit....
Building Better DDoS Mitigation
DDoS attacks have been part of the landscape for so long they can sometimes be overlooked as a threat....
Cloud Security Automation For Dummies®
Get the big picture on cloud security, in all its complexity, speed, and scale. Our Cloud Security Automation...
Fast Track Your Journey to the Cloud
The decision to adopt the cloud has been made. Your company exercised caution by electing to first adopt...
10 Benefits of Oracle's Data Management Platform
Accelerating business change begins with the proper management of an organization's data. With Oracle's...
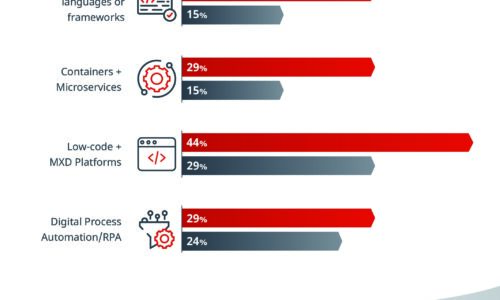
What Separates the Best from the Rest
Some IT organizations have the speed and adaptability to change course quickly when disaster strikes...

For digital sovereignty and transparency in the cloud
Shared use of infrastructure not only saves resources but also enables companies to push ahead with digitalisation...
3 Ways to Reduce the Risk of Data Loss
Amid the fast-moving digital landscape, security risks are on the rise. People, devices, and objects...
2019 IT Skills and Salary Report
The 2019 IT Skills and Salary Report provides the most informative and revealing insights into the inner...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.


