Mobility
Zero Trust Access for Dummies
As businesses continue to embrace digital innovation, cloud applications, and the new work-from-anywhere...

Modern Blueprint to Insider Threat Management
Taking a People-Centric Approach to Your Insider Threat Management (ITM) Programme. Insider threats can...

Modern application delivery for an adaptive, reliable network
See and hear how you can streamline the delivery of apps, desktops and data into a unified, fully integrated...
Securing high tech industry network data
We all understand the negative impact of data loss, so why is it that so many organisations seem to be...

Take the fight to the cybercriminals
An IT leader's guide to keeping your business running with proactive cybersecurity. It's an incredibly...

2022 Global Customer Engagement Review
Consumers expect real-time, personalized communication, seamlessly choreographed across the channels...
CRM Evolved Introducing the Era of Intelligent Engagement
Digital Transformation, a key focus of successful organizations, proves itself a business imperative,...

IDC research: Evolution of the Service Experience
How can service organizations and discreet manufacturing unearth new revenue streams, and ensure post-sales...
A Buyer’s Guide to Optimizing Remote Employees’ Extended Network
The shelter-in-place mandates put in place earlier in 2020 sent most employees home, and for the next...
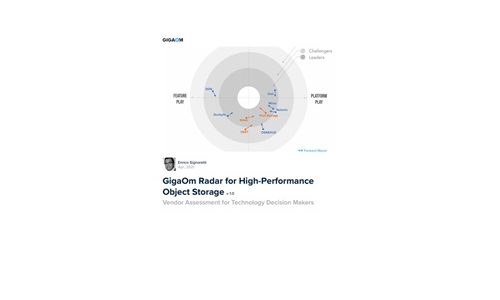
GigaOm Radar for High-Performance Object Storage
For quite some time, users have been asking for object storage solutions with better performance characteristics....

Verizon and Palo Alto Networks Enabling a Secure Connected World
Supporting mobility, minimizing the attack surface, and having reliable access to applications are key...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.