Mobility

4 Low-Code Best Practices for SAP Fiori Apps
It has been proven that enterprise IT teams that include a no-code/low-code approach for their SAP app...
Accelerate invoicing by 80% thanks to automated data processing
With the rise of digital services, data volumes are exploding. Enterprises are struggling to invoice...
A Buyer’s Guide to Optimizing Remote Employees’ Extended Network
The shelter-in-place mandates put in place earlier in 2020 sent most employees home, and for the next...

GigaOm Radar for Data Storage for Kubernetes
Kubernetes adoption is quickly accelerating, and enterprises are now in a transition phase. In the last...

The Collaboration Checklist: 8 Questions Every IT Leader Should Ask
Collaboration software can do much more than simple messaging or conferencing. Choose the right platform...
How to get maximum productivity from your remote teams
When COVID-19 struck businesses in March 2020, companies scrambled to cobble together temporary work-fromhome...
Internal Firewalls for Dummies Guide
Organizations can no longer rely on edge firewalls alone to provide network security. Once attackers...

Future-proofing endpoint management
New devices, platforms, applications, and technologies connecting to the network are overwhelming IT's...

The World is Your Workplace: Public Safety Mobile Solutions
Public safety personnel of all types rely on mobile technology to remain connected, efficient and informed....
What your business needs for a hybrid and remote-first workplace
The pandemic redefined 'work' as we know it. Companies adopted new technologies and workflows to support...
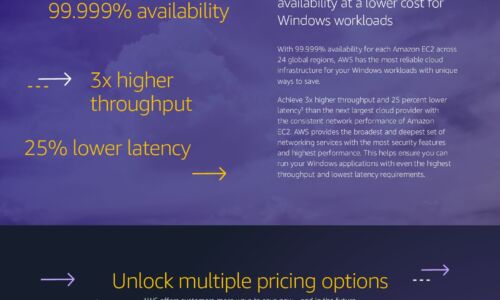
Windows Cost Savings Infographic
Save by moving Windows workloads to AWS Companies can lower infrastructure costs while improving performance,...
Empowering Medical Manufacturers to Become Leaders
Due to increasing technology and product complexity, regulatory requirements and supply chain issues,...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.