Network Infrastructure
5G for the enterprise
With a desire to better understand the current, on-the-ground reality for enterprises and organisations...
Internal Firewalls for Dummies Guide
Organizations can no longer rely on edge firewalls alone to provide network security. Once attackers...
DDoS Attack Threat Landscape — Tracking DDoS Attack Trends in Q2'22
DDoS attacks are on the rise. Ransom attacks reached an all-time high in June 2022, the Ukraine-Russia...

A Blueprint for Containers and Orchestration Best Practices
Containers enable agile deployment capabilities, requiring less coordination and oversight than on-premise...
Deliver secure, immersive gaming experiences with Cloudflare
Between growing their communities, meeting player expectations and defending against attacks, gaming...

Microsoft Digital Defense Report
Over the past year the world has borne witness to a burgeoning cybercrime economy and the rapid rise...

Securing financial services network data
Financial services is one of the most tightly regulated business sectors. The FSA, the Data Protection...
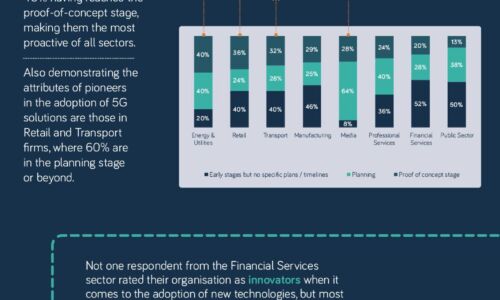
The 5G opportunity within UK industry
Neos Networks research shows that two thirds of organisations expect to have made significant investment...
Protecting commercial network data in motion
Modern organizations have become dependent upon the fixed, high-speed data networks that serve as their...

Getting Started with SASE
Secure Access Service Edge: A guide to secure and streamline your network infrastructure As enterprises...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.



