Network Security

Practical Guide To A Zero Trust Implementation
Zero Trust is becoming the security model of choice for enterprises and governments alike. However, security...
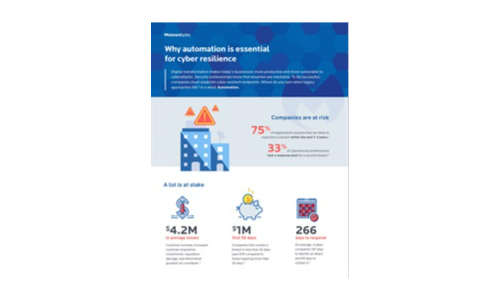
Why automation is essential for cyber resilience
Digital transformation makes today's businesses more productive and more vulnerable to cyberattacks....

Securing financial services network data
Financial services is one of the most tightly regulated business sectors. The FSA, the Data Protection...

Forrester Consulting Study: Trusting Zero Trust
The growth of ransomware and work-from-anywhere employment has created vastly greater security risks....

Encryption Is Now a Trojan Horse: Ignore It at Your Peril
The game of leapfrog between hackers and data security professionals continues. No sooner do organizations...

Isolated Castles: Incident Response in the New Work From Home Economy
Since the shift to work from home, there's been a paradigm shift in the IT and security industry. The...

DDoS in the time of COVID-19
COVID-19 has caused major disruption to business on a global scale creating the perfect storm for cyber...

The State of Email Security 2020
Global business is interspersed with a diversity of industrial sectors, united by a single, common communication...

10 Hidden Costs of an On-Premises Phone System (PBX)
Many on-premise phone system (PBX) manufacturers claim that the five-year costs of their systems are...

Five Key Enterprise Networking Trends to Watch in 2020
This IDC Market Perspective provides insights into five key trends impacting the enterprise networking...
Lessons from past vulnerability exploits and how WAF can help
Fight web attacks in seconds without slowing down your website. The onset of 2020 was marked by the disclosure...

Get a Fast Office 365 User Experience
Recommendations for a smooth migration, fast results. A Microsoft Office 365 migration can be daunting....
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.