Network
Intelligent technology for media workflows
Technology in media evolves quickly. Once seen as buzzwords, AI and machine learning (ML) are now crucial...
7 Key Considerations for Microservices-Based Application Delivery
As you modernize your applications with microservices-based architecture and Kubernetes, you must also...

SASE-Ready WAN Edge for the Work from Anywhere Era
Enterprise networks are on the verge of a major tipping point, driven by the shift from employees working...
Enhancing Teams with enterprise-grade telephony
Today's businesses depend on a robust communications experience to drive innovation, and phone calls...
DataOps: Moving Financial Services Organizations Into The New Economy
There has never been a more uncertain—yet more promising—time for financial services organizations. Global...

Cyber Security for Dummies
Protect your business and family against cyber attacks Cybersecurity is the protection against the unauthorized...
2021 Buyer's Guide to Comprehensive Cloud Security
Cyber resilience comes when you've secured your multi-cloud infrastructure and enabled your DevSecOps...
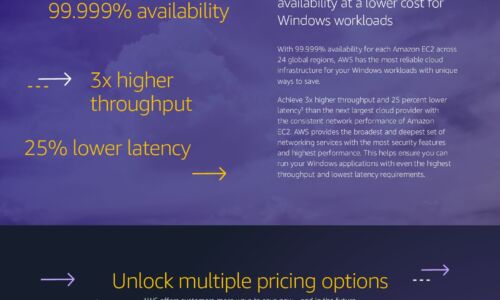
Windows Cost Savings Infographic
Save by moving Windows workloads to AWS Companies can lower infrastructure costs while improving performance,...

Get Closer in 2021: Key Trends from NRF
Another by-product of 2020 is the digital transformation that is happening within the retail industry....

Designing Hyper-Aware Industrial Facilities
At its core, the Internet of Things (IoT) is an amalgamation of machines in the physical world, logical...

A guide to the benefits of Unified Communications & Collaboration
In order to succeed, modern businesses must seek to create a workplace that delivers an exceptional customer...

Experience in action
Everybody's talking about customer experience The future health of your brands, products, and services...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.

