Network
Vössing Case Study
As a leading engineering firm in consultancy, planning, project management, and construction supervision,...

5 Remote Work Threats and How to Protect Against Them
With the surge in remote work, many IT and security teams are forced to make security tradeoffs to maintain...

Planning for Long-Term Financial Stability in Uncertain Times
In this report by The Chronicle of Philanthropy, learn key elements for nonprofit financial stability—from...
Alphabet Soup: Making Sense of XDR, EDR, NDR, and SIEM
XDR, EDR, NDR, and SIEM. They are among the most prominent acronyms in cybersecurity. But what do they...
Your Data. Their Cloud.
In today's organizations, digital transformation is a vital imperative—and cloud services offer a proven...
Transforming the SOC: Building Tomorrow's Security Operations, Today
When you think of a security operations center (SOC), what comes to mind? Is it an organized team of...
Enhanced Privilege Access Management Solutions
Privileged Access Management (PAM) is one of the most important areas of risk management and security...

Incident Response Use Cases
According to an IBM study, the vast majority of organisations surveyed are unprepared to respond effectively...
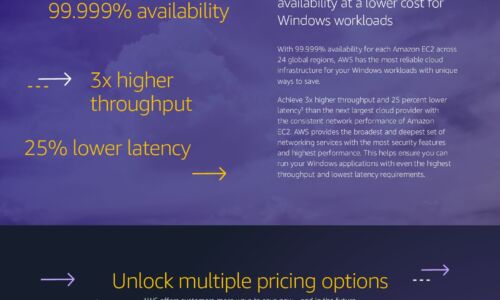
Windows Cost Savings Infographic
Save by moving Windows workloads to AWS Companies can lower infrastructure costs while improving performance,...

Cybersecurity: A Short Business Guide
The news often reports on incidents involving large corporations facing massive data breaches where the...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.