Network

SASE: Beyond the Hype
Solve network and security management challenges with a Secure Access Service Edge architecture This...

Why Corelight Is Your Best Next Move In Enterprise Security.
Despite spending billions annually on security infrastructure and services, even the most sophisticated...
An Overview of Cato Data Loss Prevention (DLP)
ata is the most valuable asset a modern enterprise has. The evolving threat landscape and shift to cloud...

Hybrid Cloud: A Smart Choice For AI And HPC
High-performance computing (HPC), once the purview of academia, is going mainstream. Often used to train...

Choose the WAF That's Right for You
Despite the industry's best efforts to bolster secure application development practices, the growing...
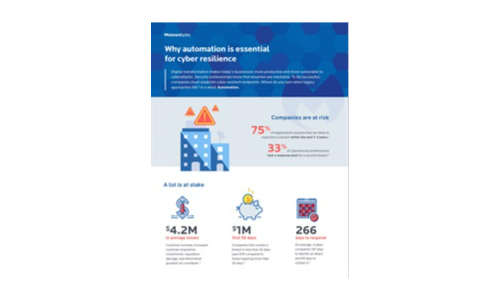
Why automation is essential for cyber resilience
Digital transformation makes today's businesses more productive and more vulnerable to cyberattacks....

How to Increase Agility with Hybrid Cloud Automation
As organizations innovate faster than ever, they bring new applications and services to market in more...
How to Build Your Microsegmentation Strategy in 5 Steps
A breach to your organization's network is not a question of if, but when. Are you prepared with a micro-segmentation...
Digital Acceleration in the line of coronavirus
A global survey of 600 technology decision-makers conducted by MIT Technology Review Insights, in association...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.