Network
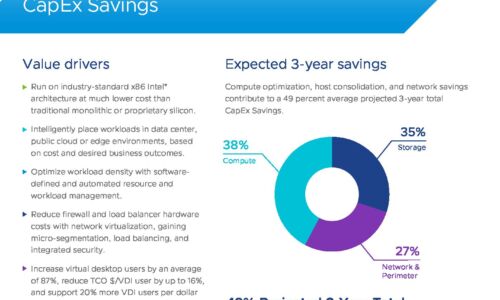
VMware Cloud Foundation: Maximise Digital Business Value
76% of IT organizations are committed to hybrid cloud as a long-term strategy to quickly adapt to changing...
Protect and Preserve Your Data from Endpoint to Infrastructure
Technology has made it possible for the world to maintain a somewhat business-as-usual stance, even when...
Better Security. Fewer Resources.
When you consider the number of headlines that appear on a regular basis about major data breaches —...

Protecting Every Edge To Make Hackers’ Jobs Harder, Not Yours
Today's users need a network that allows them to connect to any resource from any location using any...
A Pure Primer AI, Analytics and the Future of your Enterprise
Data is transforming not only businesses, but entire industries, and the world as we know it. As a global...

Spotlight: The State of the UK and Ireland Mid-Sized Business and IT
Medium-sized businesses are central to our economies, but this varied market is hard to analyse. So,...

Retail eBook
Modern MFA For Retail's Hybrid Workforce Modern retail organizations are moving data to the cloud while...
6 ways cloud computing can support your security capabilities
Embracing cloud computing forces organizations to decide between the cost-effectiveness, scalability,...

The Future of Network Security: EMEA
IT and security leaders face a transforming digital world. In order to meet the needs of an evolving...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.




