Security Solutions
From Seismic Disruption to a New Era of Success
No one could have foreseen the terrible impact of the COVID-19 outbreak on humankind. In business too,...

10 Endpoint Security Problems Solved By The Cloud Infrographic
The three challenges you're likely facing – cost and complexity, defenses that can't keep up, and overburdened...
State of Digital Transformation EMEA 2020
Prior to the pandemic, enterprises were actively migrating private applications to public clouds as well...
State of Ransomware Readiness 2022
Ransomware has become one of the primary threats to organizations of all types over the past few years....

Protecting Your Hybrid and Hyperscale Data Centers
Organizations are building hybrid data centers that consist of composable and scalable architectures....
Cybersecurity for the Modern Era
The book explores how cyber attacks and compliance issues are evolving and outlines how you can create...

Why Corelight Is Your Best Next Move In Enterprise Security.
Despite spending billions annually on security infrastructure and services, even the most sophisticated...
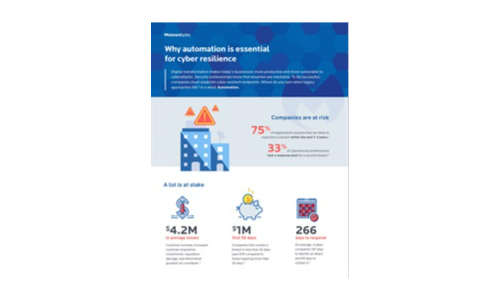
Why automation is essential for cyber resilience
Digital transformation makes today's businesses more productive and more vulnerable to cyberattacks....

Delivering Fast and Secure Enterprise Applications
Adopting a zero trust security model — authenticating and authorizing every request, device, and user...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.