Security Solutions
Implementing Zero Trust Best Practices
Network security challenges have evolved significantly over the years as users have become increasingly...

5 Best Practices for Securing Modern Web Applications and APIs
Web applications are nothing new. Neither is web application security. Many businesses have been building...

Forrester Consulting Study: Trusting Zero Trust
The growth of ransomware and work-from-anywhere employment has created vastly greater security risks....
Securely Enabling a Hybrid Cloud in Microsoft Azure
The public cloud has rapidly moved past the novelty, curiosity stage to the business critical initiative...

The Cybersecurity fail-safe: Converged Endpoint Management (XEM)
Organisations are experiencing more attacks than ever before. Cybersecurity Ventures expects a ransomware...
Filling the Gaps in Office 365
Office 365 offers a variety of choices and added functionality making it confusing for IT teams to decide...

2021 Buyer’s Guide to Comprehensive Cloud Security
Cyber resilience comes when you've secured your multi-cloud infrastructure and enabled your DevSecOps...

The SIEM Buyer's Guide for 2020
In 2020, security information event management (SIEM) solutions will be far more than an information...
Automation antidotes for the top poisons in cybersecurity management
Cyberthreats are more imminent and dangerous than ever in terms of their persistence and severity. The...

Key Steps to Optimizing Cloud Security
Do you know what's missing from your cloud security strategy? There's no question that moving to the...
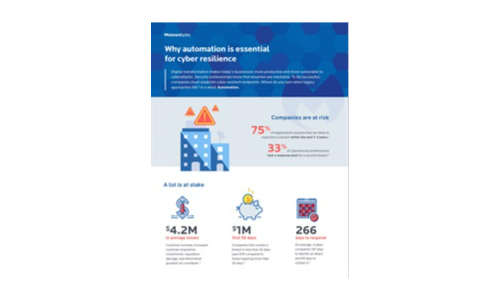
Why automation is essential for cyber resilience
Digital transformation makes today's businesses more productive and more vulnerable to cyberattacks....
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.