Server
An Integrated Approach to Embedding Security into DevOps
Organizations are adopting DevOps as a development and operational model to facilitate the practice of...

IDC: Strategies for Building Digital Infrastructure Resiliency
Multiple generations of applications. Multiple generations of infrastructure. Is there a way to reduce...

5 Reasons to Make the Shift to Cloud-Managed Networking
Cloud has proven advantages for the enterprise. Modernizing IT with cloud apps, compute, and storage...
Multi-Factor Authentication Buyer's Guide
With the increase in phishing and data breaches over the last few years, the chances are that your login...

Cloud Clarity: Don’t Let Complexity Derail Your Digital Strategy
Cloud has never been more important to agile, responsive organisations, but the reasons for its appeal...

Travel distance for parts pickup operations reduced by up to 45%
Fujitsu's Digital Annealer can solve combinatorial optimization problems instantly using a digital circuit...
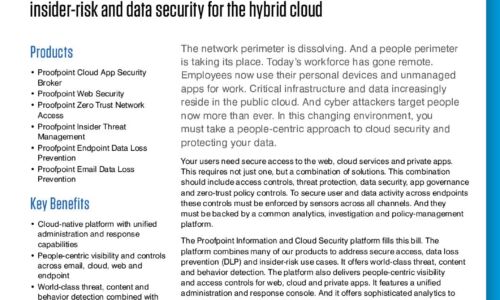
Proofpoint Information and Cloud Security Platform
The Proofpoint Information and Cloud Security platform combines many of our products to address secure...

Buyer's Guide to Comprehensive Cloud Security
Cyber resilience comes when you've secured your multi-cloud infrastructure and enabled your teams with...
A Guide for SMBs: Can I really become “less hackable”?
After nearly 20 years working in cybersecurity, I am still asked the age-old question by business owners:...

11 Recommended Security Practices to Manage the Container Lifecycle
This paper details 11 recommended practices for DevSecOps teams needing to move to a more modern application...

CISSP For Dummies
Secure your CISSP certification! If you're a security professional seeking your CISSP certification,...
Design Principles for Scaling a Global SD-WAN Network
Learn best practices for simplifying deployment and scaling your enterprise SD-WAN. ...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.