Storage

Enduring from Home: COVID-19's Impact on Business Security
Faced with shelter-in-place orders in their home counties and states, countless companies transitioned...

5 ways IT can increase employee productivity with Chrome Browser
As enterprises contine to adopt web-based apps, users spend more time their web browser than ever before. With...

The top 3 IT pains of the new reality and how to solve them
For those considering a better ITSM solution, there are powerful reasons to think beyond just that singular...
15 Ways Your Website is Under Attack
Web applications are the home of your business on the internet. The functionality within your website,...
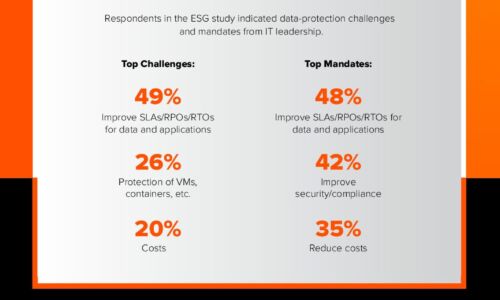
Close the Data Availability Gap
A recent ESG survey of over 1,000 global IT decision-makers found that 82% of enterprises are facing...
The evolution of process automation
Automation has a long and storied history. Today, advancements in artificial intelligence (AI) are spawning...
Effieciency, Productivity and Growth - Quickbooks Vs NetSuite
Why stay with software that holds your business back when you could use a system that empowers your business? Improve...

Business transformation through digital modernization
Amid constant changes, businesses must move rapidly to embrace new work styles. Recent research suggests...
How to Achieve Cloud Success with Hybrid Cloud Operations
A hybrid cloud operating model can provide significant benefits for traditional and modernized IT. However,...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.