VPN

2022 State of the Threat: A Year in Review
In 2022, ransomware remained the most prevalent form of attack. In investigations by Secureworks® incident...

20 Examples of Smart Cloud Security
Smart cloud security provides critical capabilities such as governing access and activities in sanctioned...

7 Experts on Moving to a Cloud-based Endpoint Security Platform
Without a doubt, endpoint security has become an urgent priority for many organizations, and it's not...

Secure Access To Over 150 Systems, For Over 2000 Diverse Users
A global leader in the field of smart energy was looking to provide better and secure remote access to...

Isolated Castles: Incident Response in the New Work From Home Economy
Since the shift to work from home, there's been a paradigm shift in the IT and security industry. The...
Understanding the Obstacles to WAN Transformation
Network engineering and operations leaders are looking to software-defined wide area networks (SD-WAN)...
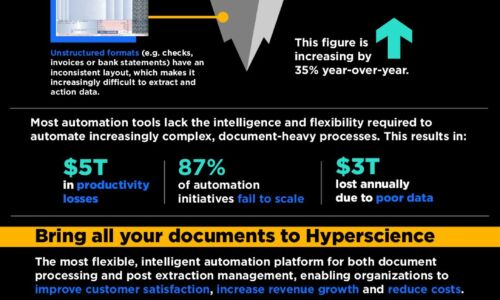
A 5-Step Blueprint for Master Data Management Success
Data is one of the most strategic assets for any business because it fuels digital transformation. The...
Securely Enabling a Hybrid Cloud in Microsoft Azure
The public cloud has rapidly moved past the novelty, curiosity stage to the business critical initiative...

Cybersecurity For Dummies
Advanced threats have changed the world of enterprise security and how organizations are attacked. These...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.