Latest Whitepapers

Hybrid Cloud: A Smart Choice For AI And HPC
High-performance computing (HPC), once the purview of academia, is going mainstream. Often used to train...

5 Benefits of Partnering with Webroot
While cyberattacks continue to evolve in volume, organization, and sophistication, security technology...
The Innovator's Guide to the Digital-first Contact Center
How do you address the Customer Experience revolution? Evolving customer expectations shape new needs...

10 Reasons to Adopt E-Signature
The way we work has changed. Modern organisations are putting together new technology systems that allow...

Best Practices in Cloud Spend Management
It's increasingly true that when cloud migration works, the world works. However, to get the full benefits...

Industrial IoT for Predictive Maintenance
Discover the benefits and challenges of Industrial IoT (IIoT) enabled predictive maintenance, and how...
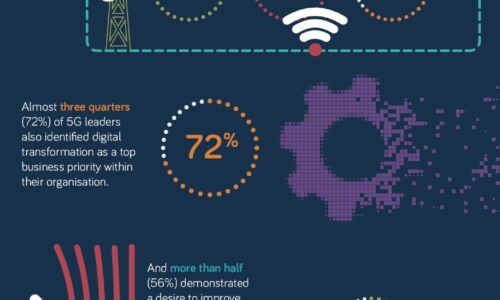
What makes a 5G Leader?
With 5G a still nascent technology, opportunity remains for businesses to accelerate adoption of this...

5 Signs You Need To Upgrade Your Phone System
If you are like most people, the sudden rush to send workers to work remotely highlighted some limitations...

A study of employee cybersecurity awareness in the Middle East
The cyber threat landscape in the Middle East is rapidly evolving, with cybercriminals increasingly targeting...
Security and Legal: An Essential Collaboration
Legal and security departments share the common goal of protecting an organisation from harm. But, while...
Four Compliance Trends For 2021
If 2020 was the year the financial services industry was turned on its head, what's in store for compliance...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.