Latest Whitepapers

High-performance persistent storage for virtualized workloads
Supporting virtualized workloads in Red Hat® OpenShift® requires reliable persistent storage that offers...

Digital transformation for UK policing
Policing in the UK is a benchmark for other law enforcement agencies around the world. Innovation across...

No Going back? The UK’s Irreversible Work / Life Shift
The urgency created by events in 2020 acted as a catalyst to faster executive decision-making and action....
Thwart cyberthreats fast with security operations + AIOps
Security operations are often managed in silos—prone to human error, manual processes and minimal visibility....

KuppingerCole Report: Privileged Access Management
Privileged Access Management (PAM) is one of the most important areas of risk management and security...

The Only Certainty is Uncertainty
We cannot anticipate change, although we can bet on its coming, be it from weather, pandemics, socio-political...

Forrester Consulting: Bridging The Developer and Security Divide
As security professionals work to create a secure environment for organizations, developers are often...

Five Ways to Reduce the Cost and Complexity of File Sharing
There are two ways a legacy technology solution gets retired. Gradually, and all of sudden. No one likes...
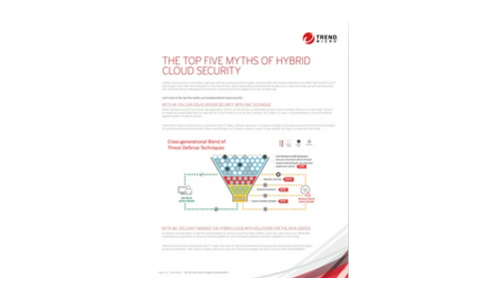
The Top 5 Myths of Cloud Security
Hybrid cloud security is a hot topic, especially with the massive growth of public cloud providers like...

New Era In Experience Report
We've all experienced the widespread impact of the COVID-19 pandemic. From a business perspective, the...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.