Latest Whitepapers

20 Examples of Smart Cloud Security
Smart cloud security provides critical capabilities such as governing access and activities in sanctioned...
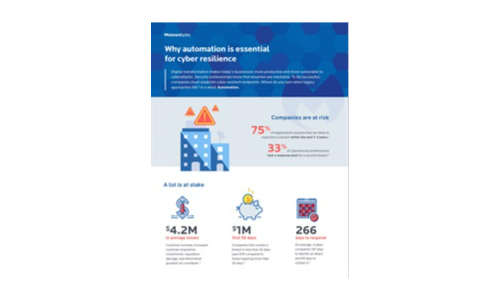
Why automation is essential for cyber resilience
Digital transformation makes today's businesses more productive and more vulnerable to cyberattacks....

Rethinking Enterprise Data Management: A 360 Degree View
The unprecedented growth in data demands enterprises to take a fresh look at enterprise data management...

Why Corelight Is Your Best Next Move In Enterprise Security.
Despite spending billions annually on security infrastructure and services, even the most sophisticated...

Security Starts Here - Privileged Access Management
The need to support safe and secure remote access for administrators, high-profile breaches (SolarWinds,...

Replace AV Buyer’s Guide
Today's businesses face a unique set of security challenges. Many organizations know their current antivirus...
How 3 Leading Organizations Took the Fast Path to Cloud
VMware Cloud on AWS Case Studies. Whether you are faced with moving specific applications to the cloud,...

How to Ensure Flexibility in a Hybrid Multicloud Strategy
Enterprises are moving rapidly to diverse cloud models, including hybrid cloud, multicloud and connected...

Modern Storage Accelerates Data Insights, Speeding Innovation
Deep learning opens up new worlds of possibility in artifi cial intelligence, enabled by advances in...

Cloud and Web Attacks
A Cloud Security Alliance Research Report Work environments have undergone rapid but lasting changes...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.









