Latest Whitepapers

M&A IT Integration Checklist: Active Directory
If your organization is involved in a merger and acquisition, the impending IT integration project might...
Filling the Gaps in Office 365
Office 365 offers a variety of choices and added functionality making it confusing for IT teams to decide...
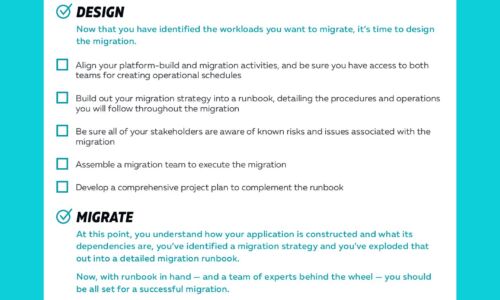
Cloud Migrations Checklist
Cloud migrations can be complex. The key to a successful migration lies in the planning. To help, we've...

Better Defenses Against Modern Bots
Four Habits of Highly Effective Malicious Bots — and how you can overcome them Bots have become easy...

2021 State of the Intelligent Information Management Industry
2021 is shaping up as a year of opportunity for many organizations in building out their information...
FOUR COMPLIANCE TRENDS FOR 2021
If 2020 was the year the financial services industry was turned on its head, what's in store for compliance...
5 Signs MDR Is Right for Your Organization
Perhaps you've been considering a managed detection and response (MDR) solution, but you aren't quite...
Boost operational efficiency with modern ERP workflows
There are several roadblocks that can stand in the way of achieving operational efficiency, including...

Accelerate full-stack web and mobile app development
Developing scalable, secure, high-performance web and mobile apps that empower users—while minimizing...

How Mature is your Content Strategy?
Brands that offer outstanding digital experiences attract and retain more customers. But it's difficult...

Your Path to Cloud Analytics: 10 Key Considerations
Now more than ever, businesses are choosing SaaS for modern analytics. That's because today's vastly...

Simplified AI: Level UP Your Decisioning
Anybody who has ever played a video game knows that to reach your end goal, whether it's rescuing the...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.