
Five things every business needs to know about GDPR
After years of preparation and drafting, the final t's were crossed and i's dotted on the General Data...
A Visual Landscape Of Cybersecurity
Our world has never moved faster in terms of cyber threats, security technology innovations and overall...
Cybersecurity for the Modern Era
The book explores how cyber attacks and compliance issues are evolving and outlines how you can create...
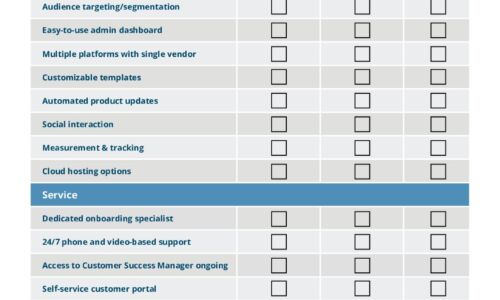
IT Comms Plan Bundle
IT teams need to communicate important messages across their organization – from scheduled maintenance...
Optimizing customer experience with payment presentment
Customer experience isn't just a buzzword. It's a differentiator. With 2.041 billion digital global buyers1...
Making the Grade: End-to-End Security in Education
While students are preoccupied with completing online school assignments and streaming educational videos,...
2021 State of Malware Report
The story of 2020 is of the devastating COVID-19 pandemic, and of how the world adapted. The story of...

Hope is NOT a strategy: Secure your business with the Content Cloud
Seems like every week there's news of another cybersecurity breach. Ponemon Institute has found that...
Financial Crime Convergence: Think Collaboration, Not Consolidation
Silos within financial crime functions are the criminal's best friend. Malicious actors have exploited,...
Seven reasons why your enterprise needs intelligent search
Organizations are hungry to use data to grow and improve performance, but enterprises are struggling...
Is Your WAF Keeping Pace with Today’s Advanced Threats eBook
As the threat landscape evolves, so must our security controls and countermeasures. Recent research from...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.


