Measuring Security Awareness Impact for Long-Term Success
Most security leaders know that an effective security awareness program can play an outsized role in...

How Proofpoint Defends Against Cloud Account Takeover
Prevent and mitigate potentially devastating cloud account takeovers. Cyber criminals are following businesses...

13 Email Threat Types To Know About Right Now
Traditional email security doesn't cut it anymore. In today's rapidly evolving environment, traditional...
Alphabet Soup: Making Sense of XDR, EDR, NDR, and SIEM
XDR, EDR, NDR, and SIEM. They are among the most prominent acronyms in cybersecurity. But what do they...
The Total Economic Impact™ Of Slack For Technical Teams
Slack commissioned Forrester Consulting to conduct a Total Economic Impact™ (TEI) study and examine...
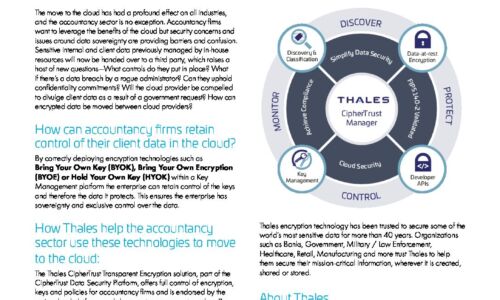
Accountancy sector - Cloud challenges
Accountancy firms want to leverage the benefits of the cloud but security concerns and issues around...

VMware Cloud Workload Migration Tools
Before starting a cloud migration project, it is critical to understand the strategies and tools available...

A guide to the benefits of Unified Communications and Collaboration
In order to succeed, modern businesses must seek to create a workplace that delivers an exceptional customer...

SD-WAN in the Age of Digital Innovation
Achieving Business Agility While Reducing Disruption. Most organisations are in the midst of some form...

8 Ways that Mobile Scanning can Improve CPG Profitability
This checklist details how CPG manufacturers can identify and address critical supply chain processes....
SaaS Security Solution Checklist
SaaS applications have provided tremendous value to end users due to their easy setup and collaboration...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.