Hardware
IoT Smart Cities & Buildings
Many of today's commercial buildings predate modern energy-saving tools and techniques. That means they...

Creating the ultimate spend-smart IT asset management system
The right technology mix for greater hardware, software, and cloud cost control. Whatever your business...
Redefining Modern Master Data Management in the Cloud
Your organization needs to continuously innovate to stay competitive. And business insights are necessary...

2021 State of the Threat in review
The State of the Threat report is compiled by the world-renowned Secureworks® Counter Threat Unit™...

The Business Value of Red Hat Runtimes
IDC has addressed organizations that have deployed Red Hat® Runtime's solutions as a foundation for...

5 Critical Requirements for Internal Firewalling in the Data Center
Preventing hackers from hiding inside large volumes of east-west network traffic has now become critical...
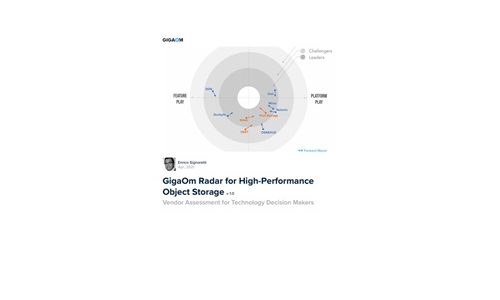
GigaOm Radar for High-Performance Object Storage
For quite some time, users have been asking for object storage solutions with better performance characteristics....
eBook: Product development strategies managed with cloud PLM
Discover how your product development strategies can benefit from modern cloud software-as-a-service...

7 Characteristics of Successful Hybrid Cloud Strategies
According to Gartner, by 2020, 75% of organizations will have deployed a multiload or hybrid cloud model....

Building A Better Cloud Begins With Better Infrastructure
The modern enterprise lives in a multi-cloud world, where delivery of infrastructure resources and IT...
IPv6 migration with Micetro by Men&Mice
IPv6 adoption has been slow in the corporate world. Despite global IPv6 traffic increasing with 500%...
Digital Transformation Today
More and more buyers are looking for a digital experience that not only improves challenges like wait-time...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.