Server
Application Protection Report 2022: In Expectation of Exfiltration
Welcome to F5 Labs' Application Protection Report 2022. As in years past, the goal of this report is...
CSI Endpoint Security Survey 2022
The unprecedented shift to remote work has changed everything. New data reveals what security professionals...
Introduction to AWS Security
Raise your security posture with AWS infrastructure and services. AWS's approach to security, including...
Redefining Data Loss Prevention
Data doesn't move itself. People—whether they are negligent, compromised or malicious—move data in...
10 Biggest and boldest insider threats
Over the last two years alone, insider security incidents have jumped 47%, with the average cost per...

5 Principles For Securing DevOps
DevOps, a new model for software development, is transforming the way the world creates software. And...
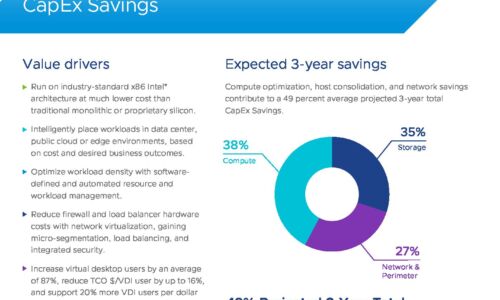
VMware Cloud Foundation: Maximise Digital Business Value
76% of IT organizations are committed to hybrid cloud as a long-term strategy to quickly adapt to changing...

Finding a Setting Worthy of Your 'Crown Jewels'
Keep all the Data in a single, unified Database – Oracle Exadata For most companies, data is critical...
Merger and Acquisition IT Integration: Active Directory
Each IT integration project is unique based on the timelines, the makeup of the environment and the goals...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.




