Server
Cloud Security Report 2022
Cloud adoption continues to permeate throughout organizations as they embrace agile software development....

Mobile Beta Testing with TestFairy
Streamline your mobile app beta testing with managed app distribution and user feedback collection. Easily...

Security Starts Here - Privileged Access Management
The need to support safe and secure remote access for administrators, high-profile breaches (SolarWinds,...
Ransomware Case Studies
Ransomware is a simple name for a complex collection of security threats. Attacks can be short and brutal,...
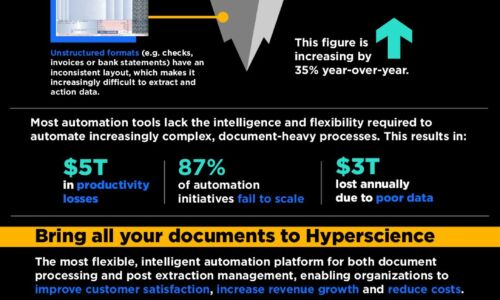
Simplify the complexity of data management
Every aspect of a business produces and requires information whether it's marketing or human resources....

The Perfect Storm: Why MDR is Your Only Option in Modern Cybersecurity
Covid, work from home, and bring-your-own-device have expanded our threat envelopes 1000X. Attacks with...
The Total Economic Impact™ Of Red Hat OpenShift Cloud Services
Modern-day companies are expected to have the capabilities, skills, and tools to support evolving customer...
8 Business Drivers That Motivate Cloud Migrations
8 Business Drivers that Motivate Cloud Migrations Why do today's businesses migrate to the cloud? At...
Rapid, Successive and at Scale
Disruption -- whether big (COVID-19) or small (new start-up competitors) -- has more or less become commonplace...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.