Server
Protect K-12 Schools from Cyberattacks with Active Breach Protection
Ransomware is not just another buzzword. It is a very real threat to educational institutions of all...

Network Security Approaches and the Case for Zero Trust
Top executives say that legacy network technical baggage is holding them back from transforming their...

Find and Protect your sensitive Data with SQL Server Complance tools
This technical brief examines a database compliance and security scenario in the enterprise. It describes...
Cyberthreats: A 20-Year Retrospective
Annual threat reports provide an opportunity to look back at significant events of the past 12 months...

Dell Docks: A Dock For Every Need
Dell Docks- giving you more power to get ahead. Designed to efficiently connect to displays, keyboards,...
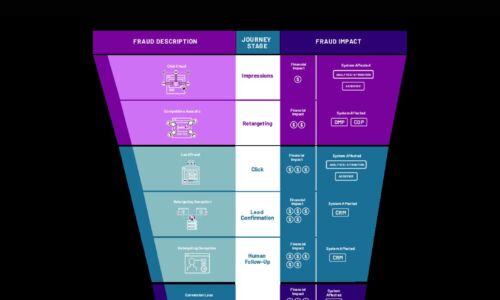
Cybercrime Threatens the Digital Funnel
Cybercriminals are employing new attack methods on new digital surfaces, including digital marketing....
The Total Economic Impact™ of DocuSign CLM
DocuSign provides a contract lifecycle management (CLM) solution that acts as a centralised, cloudbased...

Office of the CTO Report: Continuous API Sprawl
APIs are a contract between the service provider and service consumer. When any application uses an API,...

Nasuni for Rapid Ransomware Recovery
The FBI's Cyber Crime division defines ransomware as 'an insidious type of malware that encrypts, or...
Privilege Access Management Buyers' Guide
Security breaches show no signs of slowing, and credential theft is the number one attack vector. Privileged...
Take Control of Security Operations with Consolidation and XDR
The constantly evolving cyber threat landscape and steady stream of cybersecurity technologies designed...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.