Software

Active Directory Security Primer
The most important question in security is, 'Is our data safe?' If you can't answer that, it's tough...

Is Your Last Mile Technology Fit for Purpose?
The last mile is always evolving. In the new, digital post pandemic reality, delivery businesses must...

10 hot-button CX topics for financial services businesses
Learn how to break down silos and unify objectives to lay the foundation for sophisticated omnichannel...
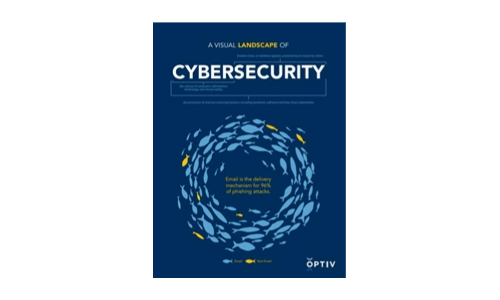
A Visual Landscape Of Cybersecurity
Our world has never moved faster in terms of cyber threats, security technology innovations and overall...

Serving hospitality at the Edge
With the pandemic now in its second year, almost every sector across the globe is still trying to overcome...
Data Governance Is Everyone’s Business
Erwin's contribution to data governance brings IT and business together for a new era in data-driven...

Protect your Data and Secure your SQL Server Database Operations
You manage hundreds of SQL Server databases spread over multiple sites and departments, even as you face...

Medium-Business Survey Highlights
In 2020, Dell Technologies and Intel commissioned IDG to conduct an online research study to understand...

Expose the Uncertainty: Best practice for reporting risk
With cyber threats increasing, it's vital for business leaders to understand and mitigate risks that...
Deliver more reliable digital services by knowing what supports them
When a critical IT service goes down in your enterprise, how can you quickly determine the root cause,...
Evolution Of The Marketer's Toolkit
More than ever, enterprise organisations need a 360-degree view of their customers to deliver the kind...
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.