Storage
Redefining Data Loss Prevention
Data doesn't move itself. People—whether they are negligent, compromised or malicious—move data in...
Know Your Options Before Moving To The Cloud
It's imperative for company and IT leaders to understand that the term 'cloud' is very broad and can...

Using MITRE ATTandCK™ in Threat Hunting and Detection
MITRE ATTandCK ™ is an open framework and knowledge base of adversary tactics and techniques based...

Manufacturers get industrial strength security with private 5G.
5G technology has quickly evolved from aspirational to businessready, and many organizations are already...
Part Five - Futureproofing your cybersecurity strategy
Payment fraud occurs when a thief steals someone's payment information to make unauthorized transactions...

Migrate, modernize, transform
To win in the digital era, companies are seeking new ways to build apps and services, connect previously...
12 Steps for Stronger Ransomware Protection
Over the last few years, we have signed up hundreds of MSPs. We like to ask every new customer why they...

Modern Storage The Answer to Multicloud Complexity
No matter what it's called or how it's described, it's a serious problem that's only getting worse. As...
Best price performance
Get the most value from your cloud infrastructure spend AWS offers the best price performance for virtually...
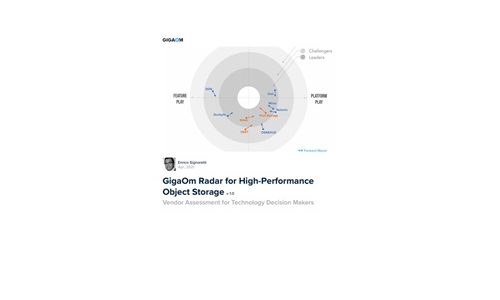
GigaOm Radar for High-Performance Object Storage
For quite some time, users have been asking for object storage solutions with better performance characteristics....
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.