Latest Whitepapers
An introduction to event-driven architectures
Learn common use cases of event-driven architectures Event-driven architectures (EDAs) enable you to...
Are you prepared... for a world where 50% is a digital nomad?
The world of work is changing. How do you support new employee demands and anticipate the future? Learn...
Unlocking collaboration in higher education
Collaboration and knowledge sharing are pillars of higher education. Instead of working in silos detached...

Building the Modern Analytics and BI Team
We are living in an unprecedented time driven by rapidly changing economic scenarios, the rise of digital...
7 Experts on Optimizing Your Security
Security teams have a difficult task to perform, and it's not getting any easier. IT environments are...

Reimagine How Work Gets Done - Introducing Fujitsu Work Life Shift
It's time to reimagine a new future. The concept of the workplace has changed forever. It's no longer...
The Total Economic Impact Of PayPal's Enterprise Payment Solutions
PayPal's enterprise solutions deliver enterprise-level credit card and alternative payment processing...

5 stages of security automation maturity: how do you compare?
Security automation has the power to help enable enterprise transformation through improving operational...

Customer journey map: The new digital-first CX
This infographic explores the linear customer journey alongside today's customer experience expectations....

Beneath The Surface Of Digital Transformation
Digital technology has changed market dynamics. Customers expect great experiences, and digital transformation...
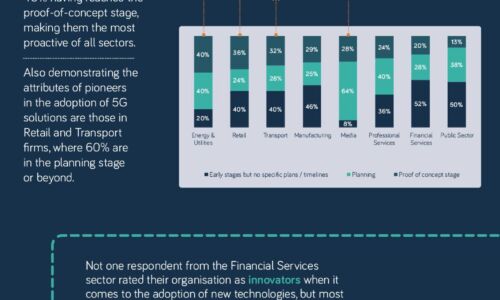
The 5G opportunity within UK industry
Neos Networks research shows that two thirds of organisations expect to have made significant investment...
Efficacy Of Micro-Segmentation Assessment Report
Micro-segmentation is an essential security control that prevents the lateral movement of attackers....
Sign up for IT Tech Publish Hub
As a subscriber you will receive alerts and free access to our constantly updated library of white papers, analyst reports, case studies, web seminars and solution reports.